June 07, 2013
— Ace On Fox. Apparently he's already burned a strawman.
He claimed that when he was speaking a few weeks ago about striking the proper balance in the war on terror he meant this. Implication: I sorta did tell you about it, you know.
Then he proceeds to swipe at the right for being interested in this, saying that we we weren't interested in it five years ago, and that it's "mature" that we now are.
Speaking of people who once had different opinions on this but whose views have "matured"...
He meant to leave but someone asked a question and he stayed to answer it. The question was about leaks. He's now gone off on a tangent, effectively blaming Congress, saying they are "fully briefed" and "empowered" to object if there's anything objectionable.
In fact that's false. As Glenn Greenwald noted the other night, Congress may be "briefed" but they're also not permitted to reveal anything they're briefed about. He had a good word for it, which I sadly forget, striking at the idea that they are involuntarily conscripted into being false supporters in such things, as they do not, in fact, have any liberty to discuss it or object openly.
Senator Ron Wyden made this point a few weeks ago.
Posted by: Ace at
08:19 AM
| Comments (334)
Post contains 224 words, total size 2 kb.
— Purple Avenger The smart ones went into hiding
Israel's Hula painted frog had not been seen for nearly 60 years, but in 2011 one was found lurking in a patch of swampy undergrowth.What's next? Giant Sloths? Monster camels in Canada? Is there a secret genetics lab somewhere recreating extinct species?Tests have revealed that the frog belongs to a group of amphibians that died out 15,000 years ago.
Openize the thread. Other than zombie frogs, I'm burned out right now.
Update: Ever wonder how evolution made roosters junk vanish? Someone figured it out.
Posted by: Purple Avenger at
07:34 AM
| Comments (131)
Post contains 112 words, total size 1 kb.
— CDR M

Mark Steyn is exactly right. Some are saying we need programs like Prism to catch the Tsarnev's and Major Hassan types (which it didn't). In reality we'd be better off just enforcing existing laws and dropping the pretense of political correctness. Nice way of tying immigration reform to the latest scandal. The Senate is still trying to pass that turd.
How did all these Tsarnaevs-in-waiting wind up living in the United States? They were let in by the Government, and many of them were let in in the years since 9/11, when we were supposedly on permanent “orange alert”. The same bureaucracy that takes the terror threat so seriously that it needs the phone and Internet records of hundreds of millions of law-abiding persons would never dream of doing a little more pre-screening in its immigration system – by, say, according a graduate of a Yemeni madrassah a little more scrutiny than a Slovene or Fijian. The President has unilaterally suspended the immigration laws of the United States, and his Attorney-General prosecutes those states such as Arizona who remain quaintly attached to them. The ID three of the 9/11 hijackers acquired in the 7-Eleven parking lot in Falls Church, Virginia and used to board the plane that day is part of a vast ongoing subversion of American sovereignty with which many states and so-called “sanctuary cities” actively collude.As for Major Hasan, who needs surveillance? He put “Soldier of Allah” on his business card and gave a PowerPoint presentation to his military colleagues on what he’d like to do to infidels – and nobody said a word, lest they got tied up in sensitivity-training hell for six months.
Posted by: CDR M at
06:46 PM
| Comments (522)
Post contains 1104 words, total size 9 kb.
— Pixy Misa
- They Quite Literally Can Watch Your Ideas Form As You Type
- The Guardian Article On The NSA Data Gathering Program
- Baltimore Center Skips WH Super Bowl Visit In Protest Of Obama's Support For Abortion
- NYT's Can Only Stay Mad At Obama for An Hour Or So
- Lois Lerner Knew Of Tea Party Targeting A Year Earlier Than Acknowledged
- China To Europe, Move Over And Shut Up
- The NSA Whistleblower Who Guessed Exactly What Was Going On Six Months Ago
- US Still Sending Military Aid To Egypt
- Trey Gowdy Tears IRS Hack To Pieces
- Syrian Gov't Forces Capture More Villages In Central Syria
- I Have A Feeling This Law Will Be Abused
- Senator Obama Sponsored A Bill That Would Have Banned Verizon Snooping
- Valedictorian Rips Up Preapproved Speech And Recites Prayer Instead
- WH Claims All This Data Gathering Isn't Aimed At Americans
- An IRS Political Timeline
- Discrimination Laws Need Taken Off The Books Or Revised To Allow For Exemptions
- NSA's Verizon Spying Specifically Targeted Americans, Not Foreigners
- Retiree Benefits And Obamacare Collide
- 1.9 Million Private Sector Jobs Created Since January 2009
- National Donut Day, Where You Can Get Free Donuts
You are hereby cordially invited to follow me on twitter
Posted by: Pixy Misa at
05:23 AM
| Comments (498)
Post contains 207 words, total size 4 kb.
— Gabriel Malor Happy Friday.
DNI Clapper rebuffed the Washington Post and Guardian stories about PRISM, saying, "They contain numerous inaccuracies," and asserting that the disclosure of the program "is reprehensible and risks important protections for the security of Americans." Notably, however, he declined to specifically identify the inaccuracies, suggesting only that the program does not intentionally target U.S. citizens. I'm reminded of the NSA "overcollection" scandal of 2009.
Turning now to the other NSA scandal, Wall Street Journal confirms that NSA has court orders to collect cellphone metadata from all three major U.S. carriers and the Democrats want you to know that this has been going on for a long, long time, so why should anyone care, amirite?
One thing that's been bugging me about this is why NSA needs this at all if its claims of being able to subpoena records are true. Brian Fung over at National Journal is thinking along similar lines:
As Marc Ambinder points out, if the NSA is already collecting metadata, why should the government need to subpoena said information to go after whistleblowers? In principle, barriers exist between the NSA (Pentagon) and the FBI (Justice Department) to prevent this sort of thing. In practice, however, the court order shows NSA was gathering the metadata on behalf of the FBI, so those barriers didn’t appear to operate as intended this time. One answer may be that even if DOJ had been able to look at the NSA’s information, it wouldn’t have been admissible as evidence in court—hence the need for subpoena. I’ve reached out to legal experts for a clearer answer, and I’ll update if and when we know more.
I don't know. On the on hand, the metadata collection was operating via court order, so you'd think the metadata would be admissible as evidence. On the other hand, it's possible NSA rules and the terms of the program require that the metadata not be used to target Americans (like James Rosen and the leaker, Stephen Jin-Woo Kim). The judicial orders were obtained under the Foreign Intelligence Surveillance Act, after all.
Happy weekend.
Posted by: Gabriel Malor at
02:50 AM
| Comments (438)
Post contains 355 words, total size 3 kb.
June 06, 2013
— Ace

These aren't firm thoughts. But I'm thinking about slowing down on first reactions.
First of all, we have to be aware that the US is not particularly good at human intelligence. Even when we were halfway decent at it, our opponent was the Soviet Union. Which, importantly, was a country. There are a lot of people in a country, and therefore a lot of potential spies.
There are far fewer people in a terrorist organization and therefore fewer potential spies. And while a disillusioned Soviet might turn spy for us, a disillusioned Al Qaeda is likely just to quit the group. Thereby taking himself out of a position where he could serve as a useful spy.
But Soviet citizens, trapped behind the Iron Curtain, couldn't quit the Soviet club. By trapping their citizens and abusing them, the Soviets made a lot of potential spies for us.
I don't think Al Qaeda does that. Again, the easiest way to defy Al Qaeda is to flee it. Not to remain in place, passing secrets to the West.
The US has never been particularly good at human intelligence, so we have made ourselves quite good at technical intelligence. This is how we've historically compensated for our so-so abilities in the human espionage realm. We've been very good at capturing signals. We famously tapped the trans-Atlantic phone cable, and thus could eavesdrop in on all phone traffic between the US and Europe (and Russia beyond).
Right now I'm thinking of Chesterton's parable of the fence.
In the matter of reforming things, as distinct from deforming them, there is one plain and simple principle; a principle which will probably be called a paradox. There exists in such a case a certain institution or law; let us say, for the sake of simplicity, a fence or gate erected across a road. The more modern type of reformer goes gaily up to it and says, “I don’t see the use of this; let us clear it away.” To which the more intelligent type of reformer will do well to answer: “If you don’t see the use of it, I certainly won’t let you clear it away. Go away and think. Then, when you can come back and tell me that you do see the use of it, I may allow you to destroy it.”This paradox rests on the most elementary common sense. The gate or fence did not grow there. It was not set up by somnambulists who built it in their sleep. It is highly improbable that it was put there by escaped lunatics who were for some reason loose in the street. Some person had some reason for thinking it would be a good thing for somebody. And until we know what the reason was, we really cannot judge whether the reason was reasonable. It is extremely probable that we have overlooked some whole aspect of the question, if something set up by human beings like ourselves seems to be entirely meaningless and mysterious. There are reformers who get over this difficulty by assuming that all their fathers were fools; but if that be so, we can only say that folly appears to be a hereditary disease. But the truth is that nobody has any business to destroy a social institution until he has really seen it as an historical institution. If he knows how it arose, and what purposes it was supposed to serve, he may really be able to say that they were bad purposes, or that they have since become bad purposes, or that they are purposes which are no longer served. But if he simply stares at the thing as a senseless monstrosity that has somehow sprung up in his path, it is he and not the traditionalist who is suffering from an illusion.
I don't know why the fence was built and I'm wondering if we should slow down on calling for its demolition until we know better why it's there and what functions it may be serving.
Given that I think we probably have little actual human intelligence on Al Qaeda, and even less on our recent plague of Leaderless Jihadis, and are not likely to get very much better at that sort of thing, technical means of collection are probably our only real source of intelligence and we might need to hesitate before foreswearing this avenue altogether.
It might be that different versions of this are palatable, and others unpalatable, and, knowing so little, we don't know which this is. I think the creepiest thought is that there is a human being reading our emails. That is creepy, because human spies, human voyeurs, are creepy.
But what if the program were such -- and when I say "what if," understand I have no idea if it works this way; I am simply speculating about one possible configuration -- that automated non-human algorithms searched for certain keywords and, generally, signs of either a foreign language or English being written by a non-native speaker. And what if the traffic so identified was kicked up to a higher level of automated scrutiny-- still no humans reading -- and scanned for additional worrisome signs.
And then, only after the billions of messages had been screened down to Worrisome Few, say a few thousand in a month, would humans then check the flagged passages, and then, if they thought those passages were alarming, seek a judge's warrant to read the full text, and not just the flagged sentences and phrases.
Now, I think that such a system would be far less worrisome, although it would still be creepy, and of course still prone to great and serious abuse.
On the other hand, I'm pretty sure that if we abandon our advantage in the realm of computer processing power (and the incredible advantage we have in that most internet traffic, world-wide, circulates through the US), I think we're going to be down to our human capabilities which, once again, I think are virtually non-existent with regard to Al Qaeda. I think we'll be down to the felt.
I don't know. We need to know more, obviously.
Posted by: Ace at
04:31 PM
| Comments (639)
Post contains 1027 words, total size 6 kb.
— Maetenloch
Today has been an insanely hectic day and now I have to rush off to a CNC class. So use imagination to fill in missing word and not complain to Maetenthak who busy making magic boomsticks.
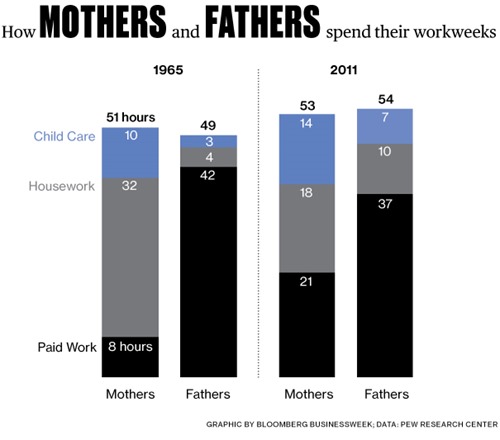
How Mom and Dad Spend Their Time (1965 vs 2011)
more...
Posted by: Maetenloch at
05:42 PM
| Comments (909)
Post contains 186 words, total size 5 kb.
— Ace A picture of the brief note at the link; here's what he wrote:
"Our landings in the Cherbourg-Havre area have failed to gain a satisfactory foothold and I have withdrawn the troops. My decision to attack at this time and place was based upon the best information available. The troops, the air and the Navy did all that Bravery and devotion to duty could do. If any blame or fault attaches to the attempt it is mine alone."
If President Obama had been in command of the D-Day operation, it would have obviously failed catastrophically, and this note would have contained the phrases "Just read about it from the newspapers," "a few rogue front-line soldiers," and "spontaneous demonstration due to an anti-Nazi 'talkie.'"
Our leaders have gone from having iron at their cores to having a cheap sheen and some glitter at their surface.
Best Detail: JPS notes that Eisenhower didn't hide behind the "mistakes were made" passive voice.
My favorite detail: He originally wrote "and the troops have been withdrawn." Then he struck that out and wrote, "and I have withdrawn the troops."
Posted by: Ace at
03:16 PM
| Comments (150)
Post contains 212 words, total size 1 kb.
June 07, 2013
— Ace
Two life coaches killed themselves together. Hahahahahahahahahaha cnn.com/2013/06/06/us/Â…
— rebecca smoochie-g (@duchessrebecca) June 6, 2013
The link is there, if you want it, but I think you have the bulk of the story right there.
Here's the thing: Those were my life-coaches. So I'm a bit without a rudder now.
Is crack a good idea? They said it wasn't but, you know. Consider the source.
Posted by: Ace at
07:47 AM
| Comments (305)
Post contains 69 words, total size 1 kb.
June 06, 2013
— Ace The "He's trying to burn us out on scandal" theory just got updinged 300 times.
Don't worry, though: It's just some "meta-data" that shouldn't concern you.
And by "meta" I mean "everything."
Graphic Omitted: You'll have to hit the link to see the graphic, if you want.
It turns out that anyone working for the government could get into trouble if they read something marked Top Secret -- even if it's on the pages of the Washington Post.
So, I've taken it down off the site. It's still over at the Post, though.
Posted by: Ace at
02:31 PM
| Comments (465)
Post contains 125 words, total size 1 kb.
40 queries taking 0.1884 seconds, 148 records returned.
Powered by Minx 1.1.6c-pink.